Zero trust this, zero trust that. You hear it almost every time someone talks about cyber security. What exactly is it though? And why should you trust something with the name of zero trust?
Zero trust cyber security is an IT security model that doesn’t trust anyone. That’s what’s good about it. It requires every person and device to strictly verify their identity before being allowed to access resources on private networks. Essentially, it is a holistic approach to network security. It does this by integrating different principles and technologies. What exactly does this mean?! It took a lot of reading for me to understand what this is all about.
What is Zero Trust Cyber Security?
First of all, the traditional cyber security works by making it difficult for those outside a network to gain access to it; but if anyone is inside it, they’re automatically trusted. You can see the obvious fault in this approach. If someone who shouldn’t be in that network somehow gains access, they’ll be able to do anything they want once they make it in. It gets even worse now that data is no longer just stored in a single place. It’s all in the cloud nowadays. And that means that it could be spread amongst multiple vendors, meaning one security control is not going to be enough.
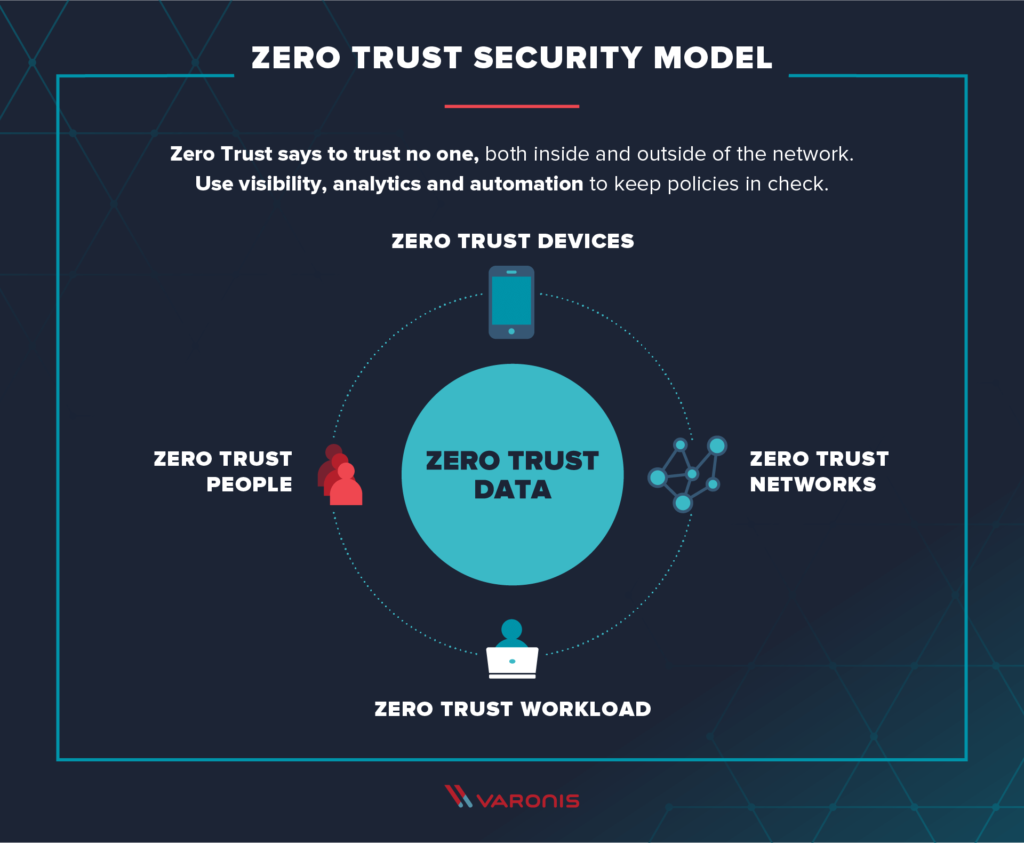
Like I mentioned above, zero trust cyber security means that no one is trusted by default, whether they’re inside or outside the network. Verification is required regardless. You want resources? You verify. Because of the success of this method, many organizations are starting, or more than willing to start, adopting this policy. This should come as no surprise, as data and security breaches can cause millions in losses for the company in question.
When Did It Start?
I couldn’t really wrap my head around the name “zero trust”. It was coined by an analyst at Forrester Research Inc. back in 2010. After that, Google implemented it in their network and of course this led to everyone else wanting in on it. It’s now a core component of secure access service edge (SASE) solutions. SASE, pronounced “sassy”, combines the software-defined wide area networking (SD-WAN) capabilities with security. It’s adjustable, it’s flexible, and that’s good.
If you’re still a little adrift, there’s some good news. It’s really easy to implement a zero-trust security system on your network. Still want to know how it works? Alright. The idea behind a zero trust network is that your network could get attacked from inside or outside of it. This means, trust no one. Another important principle is implementing “least-privilege” access. Give users the access they need, only that much. Not sure what that means? If you’ve ever seen crime or spy shows, you’ll have heard the term “need to know”. It’s the same thing.
Micro-Something
Separating into small pieces, wait no, microsegmentation. That’s what I was going for. It’s when you divvy up security perimeters into little zones. This helps to keep access separate for different parts of the network, making sure no single person or program can access everything whether they came from within or without, without separate authorization.
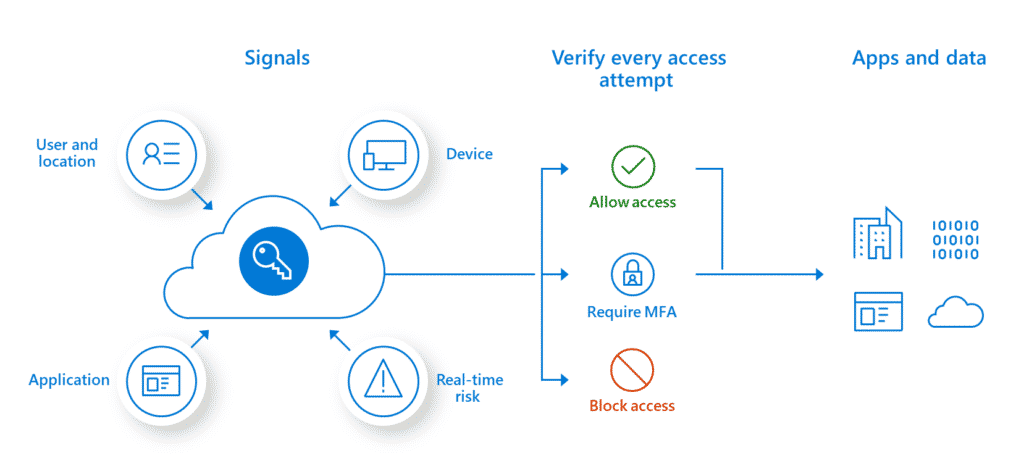
Multi-Factor Authentication
There’s another M to talk about and that’s multi-factor authentication. Simply put, it means to require more than just a single piece of evidence to prove that you are who you say you are. For example, when you’re renewing your passport you’ll need at least 3 separate sources of identification to prove it’s your identity. Even I’ve noticed one of the most common applications of multi-factor authentication (MFA) used by Facebook, Google, and Steam (for you gamers out there). For Facebook and Google it’s still optional, but for Steam it is required and they even have a separate application called Steam Guard for this purpose. Other than inputting a password, I have to enter a code sent to the Steam Guard application on my mobile phone to provide the two pieces of evidence needed to prove I’m me.
Minimizing Attacks
Zero trust cybersecurity also controls how many devices have access to a network. Kind of like how Netflix limits the number of devices you can use on your account. This helps to minimize attacks on a network.
Other than providing a better, in terms of security, environment, the main and most important benefit of zero trust cybersecurity is that it goes beyond the mere limits of firewalls and the normal perimeter based network security. It’s accurate, it’s effective, and it’s what we all need right now and for the foreseeable future. If you’d like to follow up on more about this topic or consult on how to get it implemented, don’t hesitate to contact us.

